Google trends tells us that the global Google search for “Covid-19 vaccine” reached the maximum search interest around the world this week (Figure 1). This personal interest in vaccine developments is paralleled by the interest of malicious cyber criminals and nation-state actors, who seek to exploit vaccine procurement for information, disruption and financial gain. For perspective, Johnson & Johnson’s CISO has stated that healthcare organizations are seeing cyber-attacks from nation-state threat actors “every single minute of every single day”. The stakes are obviously high, so this subject deserves notice.
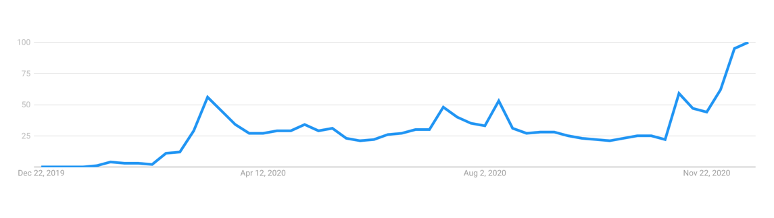
Figure 1 – Google Trends for “Covid-19” Google search
To administer vaccines, temperature-controlled transportation through a supply chain called a “cold chain” is vital. For example, Pfizer’s Covid-19 vaccine must be stored at -70 degrees Celsius, so the “cold chain” keeps the vaccines at that temperature during transportation. Given the organizational complexities involved in achieving this, the “cold chain” is ripe for exploitation.
Interpol has pushed a security alert, warning that organized cybercrime syndicates (as well as real world crime syndicates), are likely to disrupt vaccine supply chains for financial gain. Subsequently, both the FBI and the Department of Homeland Security issued a joint security alert on December 3rd highlighting the salience and severity of the risk of infiltrating the “cold chain”. The threat of nation-state attacks looms large, because they are typically patient, well-funded and sophisticated.
IBM reported this month that the international vaccine supply chain has been targeted by cyber-espionage, aimed at the delivery “cold chain” and also manufacturing of cold chain equipment. The sophistication of the methods begs the conclusion that nation state actors are the one’s behind it. The campaign likely began in September, when phishing emails were sent out across six countries, targeting organisations linked to the Cold Chain Equipment Optimisation Platform (CCEOP) of Gavi, the international vaccine alliance. Gavi partners with the World Health Organization, UNICEF, the World Bank and the Bill & Melinda Gates Foundation to help distribute vaccines to some of the poorest regions.
More specifically, campaigns have attacked several organizations in the “cold chain” through spear-phishing: an organization that monitors the movement of medical supplies across borders, a company that manufactures solar panels used for solar-powered vaccine transport refrigerators as well as a petrochemical company that manufactures dry ice used in vaccine transportation. The attackers directed phishing emails to executives at the respective companies using a spoofed identity of a business exec from Haier Biomedical (a Chinese company which is part of the UN’s official Cold Chain Equipment Optimization Platform (CCEOP) program), according to IBM. The emails contained “Requests for Quotations” to Covid-19 vaccine executives, containing malicious HTML attachments for “credential harvesting” attacks and steal login and passwords.
We have already seen attacks at the research and development phase for IP theft
There have been attacks on Covid-19 vaccine research, targeting the vaccine producers directly. This month, documents and materials related to Pfizer/BioNTech Covid-19 vaccine were stolen in a cyber-attack on the European Medicines Agency (EMA). The source? The sophisticated criminal ransomware operations or (more likely) nation state attackers.
Also, at very start of the supply chain, the vaccine manufactures are often rife with exploitable vectors with poor controls. For example, a few days after receiving permission to start final-stage trials for a Covid-19 vaccine, one of India’s largest pharma companies suffered a cyber-attack and had to shut down plants in a few countries.
How can companies involved with vaccine manufacturing and “cold chains” — and beyond — protect themselves against cyber threats?
1. Refine your threat hunting skills and enhanced privileged access management. Make sure your security operation centers are ready for anything. Consider tools that make your security operation center resilient, like Penfield.AI’s automation of threat distribution so that analysts most equipped to deal with a given threat is responding to it ASAP.
2. Strengthen your Security Operation Center. Penfield.AI offers real time training modules for your analysts to help them succeed.
3. Network segmentation
4. Conduct email security training
5. Implement multifactor authentication
6. Investigate the cyber posture of 3rd parties
7. Be prepared for the worst with a response plan: rehearse your reliance playbook
Written by: Madeleine Gottesman
See the original article here.